Guide: Using Okta Verify with third-party TOTP (Google Authenticator, FreeOTP, etc.)
Okta is an identity management and single sign-on cloud provider. Okta supports multi-factor authentication through multiple mechanisms, but at my site, only the proprietary Okta Verify smartphone app was supported.
Thankfully, Okta Verify operates via the ‘industry standard Time-Based, One-Time Password Algorithm (TOTP)’, and so can be used with standard TOTP applications, such as Google Authenticator and FreeOTP, though gaining the means to do so is slightly obscure.
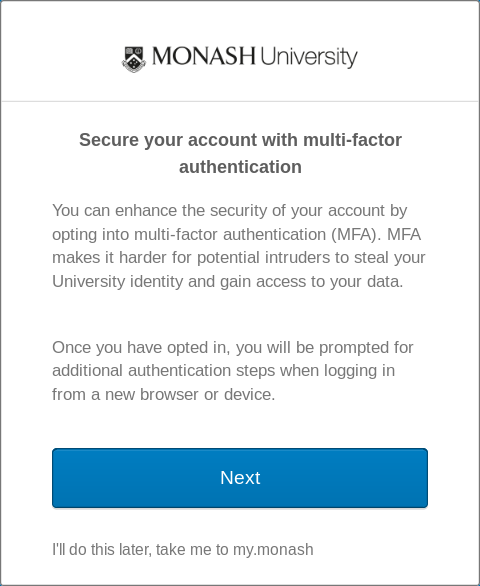
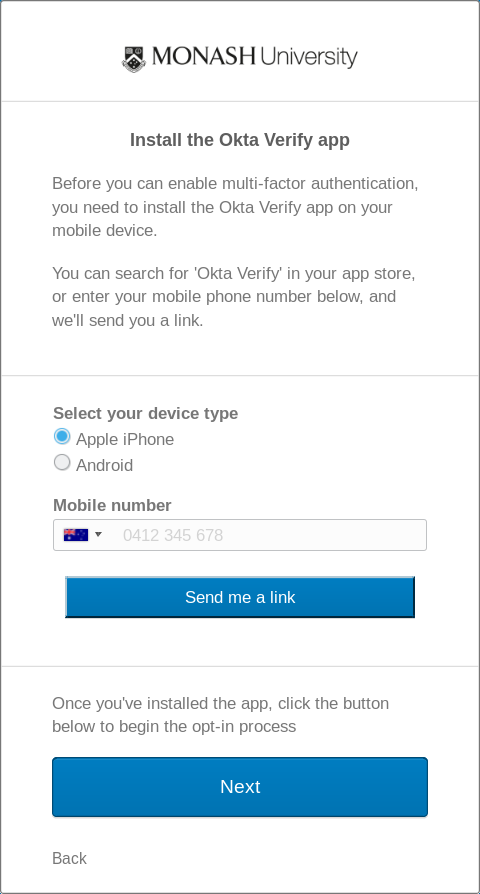
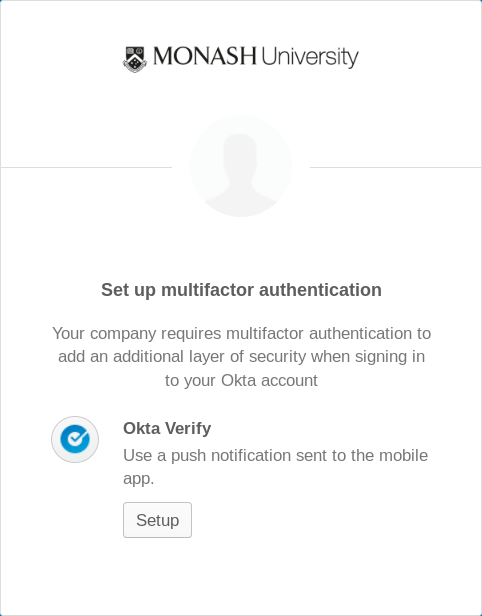
To use Okta Verify with a third-party TOTP app, proceed through the multi-factor authentication opt-in process as usual, acting as if you have installed the Okta Verify app.
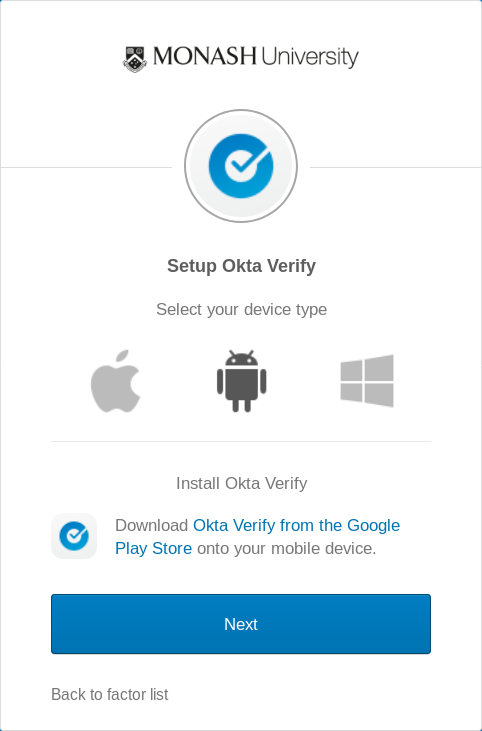
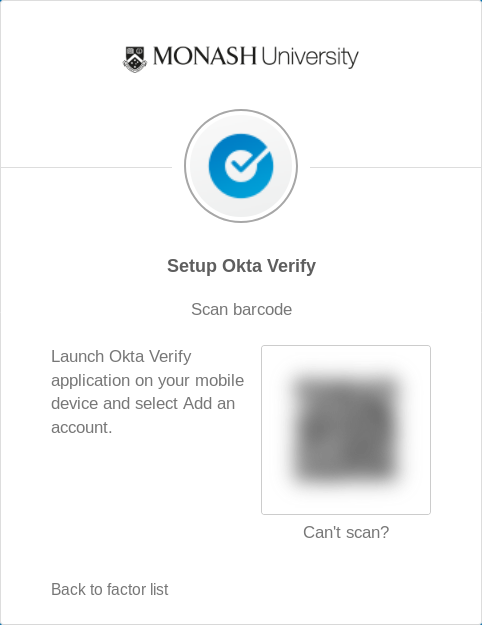
Once reaching the ‘Scan barcode’ step, ignore the barcode as this is in a non-standard format that cannot be used by standard TOTP apps. Instead, click the ‘Can't scan?’ option and select ‘Setup manually without push notification’. This will reveal the TOTP secret key.
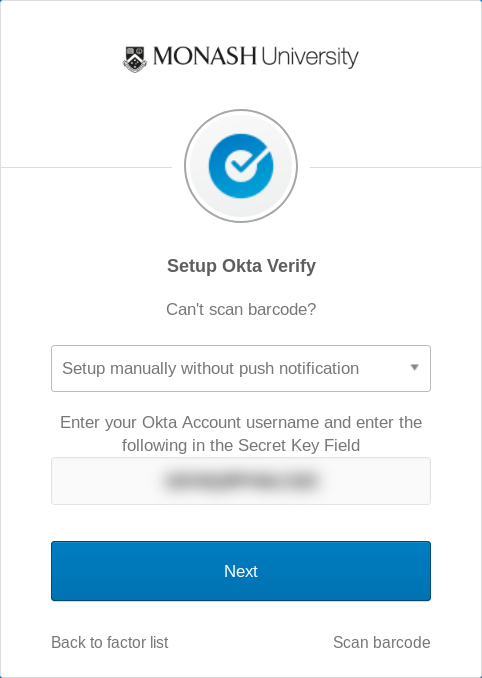
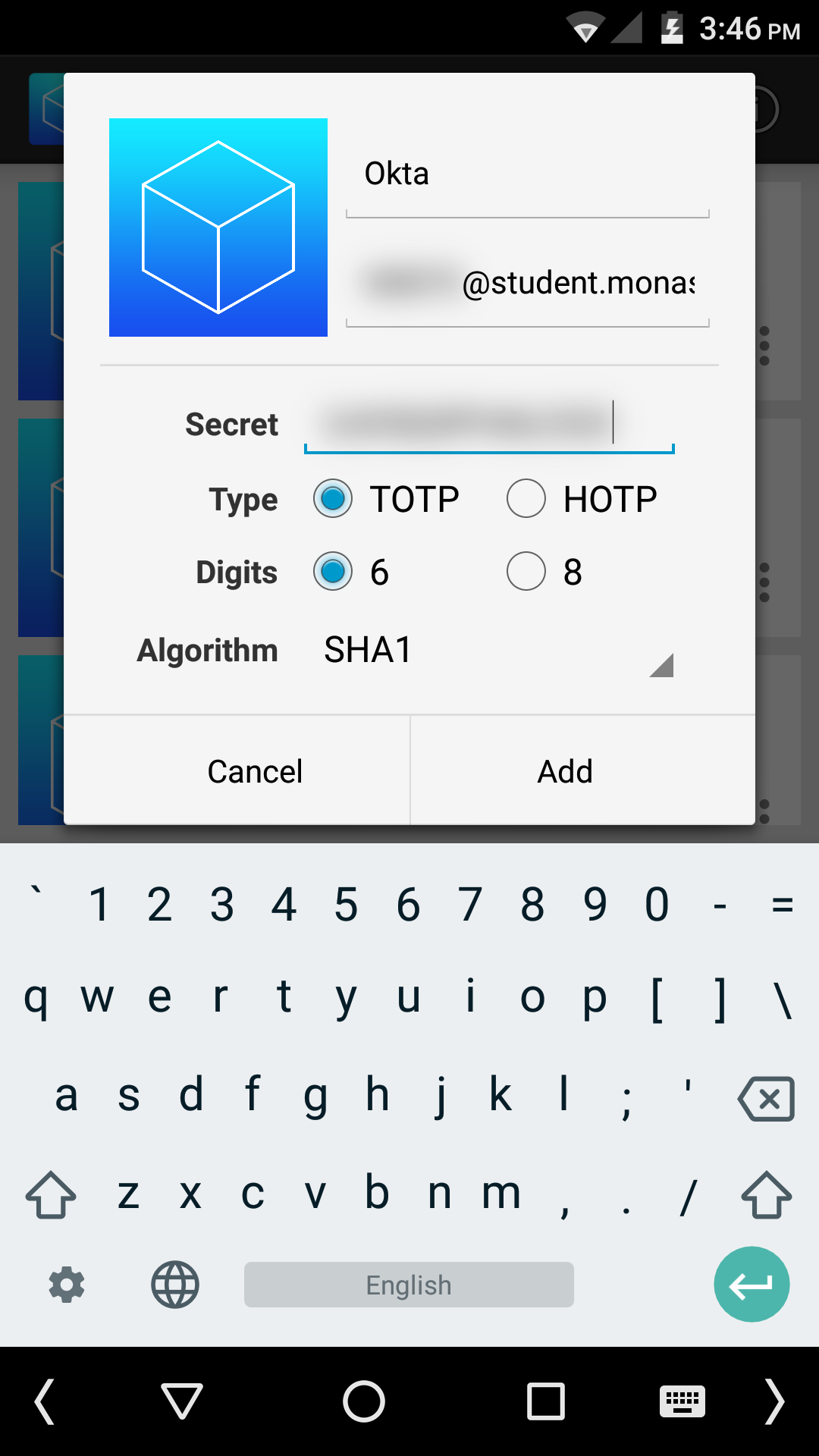
Enter the secret key into your TOTP app as usual. For FreeOTP, tap the ‘key with a plus’ button from the menu bar. For the issuer (first box), enter any text. For the account (second box), enter your username/email. For the secret, enter the secret key shown in Okta.
Leave the remaining options at the defaults. This should be TOTP, 6 digits, SHA1.
You can now use the newly-added key to generate a six digit code and finish setting up Okta multi-factor authentication.
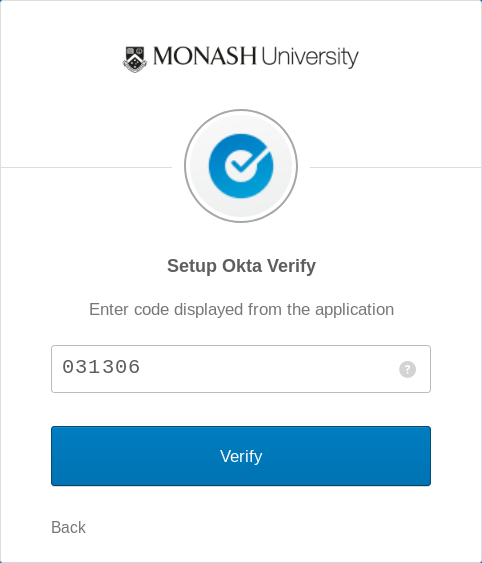
The same key can be used in the TOTP app when signing in with Okta.